Recently I published book on how search engine optimization works. This contains beginner guide on how to improve your search engine rankings. Starting a site is now a common work-from-home enterprise. But if site doesn’t look on first top pages of search engines afterward website is actually not worth and useless. This book includes a frequent guide about what it really takes to bring your website on top of search engines and why some sites always make towards the very top of search engines.
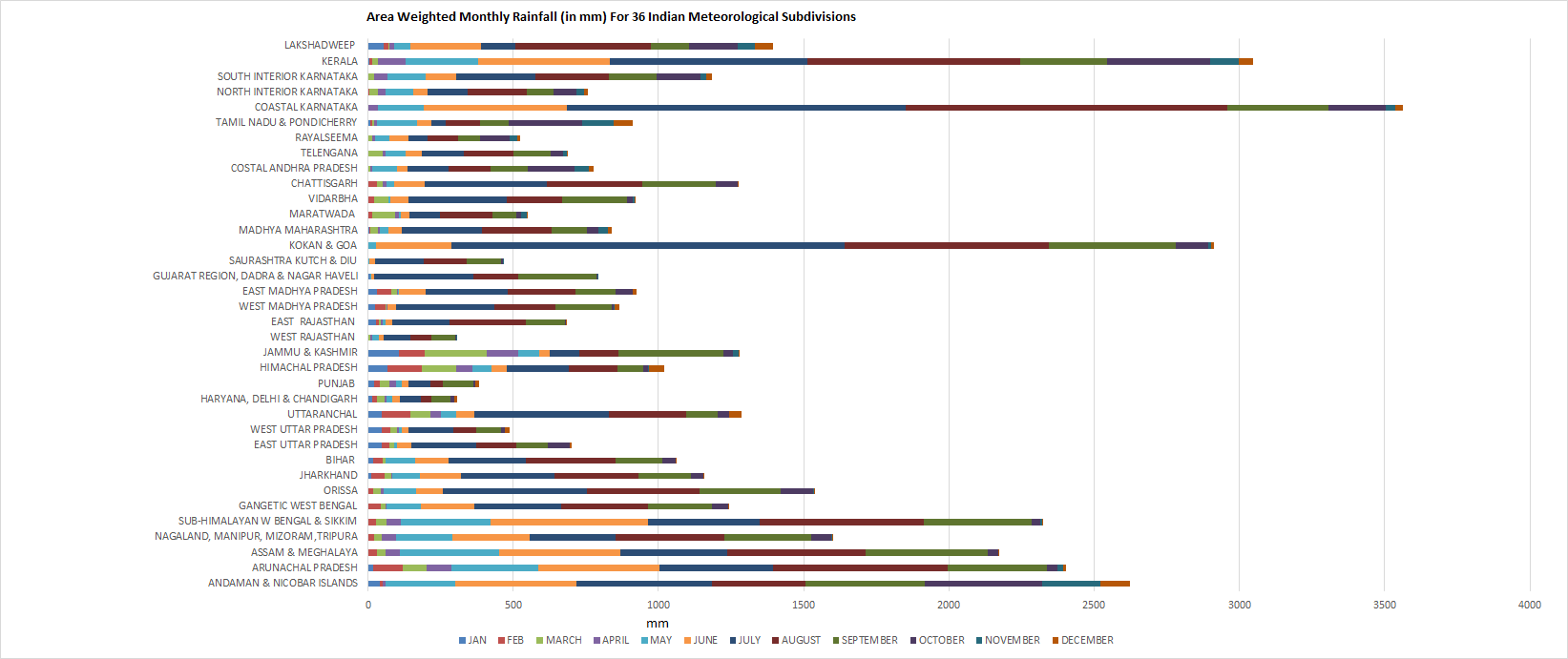
Area Weighted Monthly Rainfall (in mm) For 36 Meteorological Subdivisions
Following chart shows monthly rainfall read data in millimeter for 36 Indian meteorological subdivisions for year 2014.
Data Source: Govt of India.
Computer algorithms list
I worked some years back on computer algorithms and had list handy with me. I see many people looking for types of algorithms like network or binary tree. Here is the list for them,
Binary Search
Breadths – frist search
Fibonacci series
Bubble Sort
Quick Sort (Randomized algorithm)
Merge Sort (divide and conquer methodology)
Insertion Sort
A search algorithm or A* algorithm
Selection Sort
DIjkstra’s Algorithm: Shortest path
Heap Sort
Depth-first search
Naïve bayes
Bezier Curve
Huffman Coding (greedy algorithms
RSA (Rivest- Shamir- adleman)
Radix Sort
Prim’s Algorithm (Minimum Spanning trees)
Kalman filters
DES (Data Encryption Standard)
Kruskal’s Algorithm (Minimum Spanning trees)
Randomized sorting/Monte Carlo algorithm
Bucket sort
Bellman- Ford Algorithm (single source shortest paths)
Counting Sort
Topological sort
Bresenham line algorithm
Chinese remainder theorem
MD5 Algorithm
Phong shading
Knuth-Morris-Pratt Algorithms
Flood fill algorithm
Strassen’s algorithms for matrix multiplication
Boyer-Moore Algorithm
Floyd-Warshall algorithms(All pairs shortest path)
DDA Line drawing algorithm
Cohen-sutherland outcode algorithm
Gouraud shading
Ford-fulkerson method
Boundary fill algorithm
Rabin-Karp Algorithms
Time series algorithms
Graham’s Scan
Maximum bipartite matching
Z-Buffer Algorithm
Bidirectional search
Johnson’s algorithm for sparse graphs
Sutherland hodgman algorithm
Cyrus-Beck algorithm
Merging networks
Vertex-Cover algorithm
Tournament Sort
Introsort
Depth limited search
Greedy best-first search
Mid point circle drawing algorithm
Jarvis March
Markov chain Monte Carlo algorithms
Pre flow-push algorithms
Uniform cost
Iterative depenning depth –first search
Variable elimination algorithm
Depth sort algorithm
Zero-one principle
Backface detection
EREW Algorithms
Weiler-atherton algorithm
Bitonic sorting network
Appel’s algorithms
Warnock’s algorithm
CRCW Algorithms
Memory found heuristic search
Graphplan algorithm
Lifet-to-fornt algorithms
Exchange Heuristics
Halftoning ray tracing
Growing tomatoes plant and its fertilizer and Irrigation schedule
I recently attended one of the biggest agriculture expo in Baramati, India. It offered various innovations in Agriculture industry. I got a brochure contains Irrigation schedule, Dripping schedule and insecticide for tomatoes plant in this expo and thought to share with agriculture lovers. This was provided free of cost and agriculture enthusiastic can follow this schedule to maximum production of Tomatoes plant. Below picture is taken from tomatoes plantation which followed below plantation schedule.

Dose for One Acre
1) 10:26:26 – 4 bags
2) Single super phosphate – 5 bags
3) Potash 4 bags
4) Secondary liquid food – 2 bags
5) Humi G 20 Kg
6) Namato G- 20 Kg
7) Fungi G- 20 Kg
8) Borchol – 10 Kg
9) Sanvardhan – 10 Bags
Tomatoes Dripping Schedule
1) Before plantation of tomatoes, percolate below
Blue magic 1 liter + flora 250ml + Nimntosan 1 kg
2) During plantation of tomatoes
Flora 250gm + Funginil 1kg + Carbendazim 500g drenching
3) 2 days after plantation of tomatoes
Vruddhi 1litre + Flora 250gm
4) 5 days after plantation of tomatoes
Funginil 500gm + 19:19:19 2kg
5) After 10 days of tomatoes plantation
Magnifert 500gm + Zinfert 1kg + Silica fert 1kg + Chlorpyrifos 1 Liter
6) 15 days after plantation of tomatoes
Bluemagic 1litre + Nimatosan 1 kg + Flora 250gm
7) 20 days plantation of tomatoes
12:61:1:00 3kg + Combifert liquid 1 litre
8) 25 days after plantation of tomatoes
Silica fert 1kg + Chlorpyrifos 1litre
9) 30 days after plantation of tomatoes
12:61:1:00 3kg + Borocrop 1 kg
10) 35 days after plantation of tomatoes
13:40:13 3 kg + calcifert 500gm
11) 40 days after plantation of tomatoes
12:61:00 3kg + Flora 250gm
12) 45 days after plantation of tomatoes
00:52:34 3kg + sizer 2litre
13) 50 days after plantation of tomatoes
access 1 litre + Cabfert 500 gm
14) 55 Days after plantation of tomatoes
19:19:19 3 Kg = Vruddhi 1 litre
15) 60 days after plantation of tomatoes
Chlorpyrifos 1litre + Nimatosan 1kg + Blue Magic 1 Litre
16) 65 Days after plantation of tomatoes
12:61:00 3KG + Magnifert 1Kg
17) 70 Days after plantation of tomatoes
00:52:34 3kg + SIzer 2 litres.
Tomatoes Fertilizers for one litre water
1) 5 days after plantation of tomatoes
Ecoside 2 ml + Dymithate 1 ml + Funginil 2 gm
2) 7 days after plantation of tomatoes
Voyrosan 2gm + butter milk 5ml + zincfert + Nimisyde 2ml + Vruddhi 3ml
(Minimum 8 to 10 days once sprinkling is required)
Karpa for tomatoes plant (for one litre water)
1) Liquid bordex 1ml + Bacterisan 1.5gm
2) Carbendazim 1gm + Blue Magic 1ml
3) Bacterisan 2gm + Tebuconazole 0.5 ml
4) Blue Magic 1ml + Funginil 2gm
5) Bacterisan 2gm + Propiconazole 0.5 ml
Should be sprinkled once in 7 days.
Insecticide for Tomatoes plant (for one litre water)
1) Imidacloprid 0.5 ml + Ecocyde 2ml
2) Nimisyde 2ml + Deltamethrin 1ml
3) Larvasida 1ml + Dichlorvos 1ml
4) Ecocyde 2ml + Thymithoczyme 0.5 gm + Lamda Cyhalothrine 1ml
5) Nomaite plus 2ml + Ithian 1ml
6) Nimisyde 3000ppm 1ml + spinosad .30 ml
7) Should be sprinkled once in 7 days.
For flowering of tomatoes plant (for one litre water)
1) Growsteam 1ml + Cabfert 1 gm
2) Growthsteam 1ml + Borocrop 1gm
3) Brosofit 1ml + ZIncfert 1gm (7 days after flowering)
For tomatoes fruit setting (for one liter water)
1) Sizer 3ml + cabfert 3ml
2) Access 2ml + Silica Fert 1gm
3) Brosofit 1ml + Calci Fert 1mg ( should be sprinkled in an interval of 5 days)
How to avoid cyber attacks without antivirus
Cyber attacks are becoming very active in today’s world. Top IT companies are buying expensive products to protect their private document. Such expensive softwares are beyond common man’s budget. Below are some tips that will help to protect comman man from individuals.
1) Clear your browsing history: Regardless what browser you use, every browser has capability to store or automatically clear internet history. So you can do so by going to brower option and then navigating to privacy option. Just simply click on clear browsing history to clear your surfing history. There is an option to clear browsing history as soon as user close the browser. So you can choose any suitable option to clear your internet history.
2) Do not install freeware: Freeware are mean for adversiting and collect information. Some free software also has ability to collect information from computer and send it over the internet at regular intervals. To avoid this, do not install any freeware or any lurking softwares.
3) Close your internet: You should close your internet as soon as you have completed browsing work. It is like switching lights off when you do not need it. Keeping internet open will let other intruders/hackers to steal personal information from computer without evening noticing you.
4) Backup your data with password: It might happens a service repair team that visit your house to repair laptop/computer could steal your private data without your notice. There are some USB sticks that copies data automatically as soon as they are plugged in. So make sure to make your all backup data password protected.
